Is it safe to use one phone number everywhere?
No, it’s not safe. Your digital existence becomes a single point of failure if you use the same phone number for everything. If that number gets leaked, hacked, SIM-swapped, or spammed, every account tied to it can be affected, including banking, WhatsApp, email recovery, and shopping apps.
Today, your phone number is more than contact information. Several services may become inaccessible due to the compromise of a single key.
The Risk of Using One Number Everywhere
Your phone number has quietly become the most important part of your online identification. It checks accounts, lets you use one-time passwords, and links up your personal and financial lives across different platforms. Most people use it again and over again without realizing how connected everything has become.
You can’t just change your number like you can with a password without affecting a lot of things. The repercussions will continue for a long time if the information gets out. Spam, phishing attempts, and identity theft can go on for years.
It connects:
- Banking OTPs
- Email recovery systems
- Social media logins
- WhatsApp verification
- UPI and payment apps
- Delivery platforms
- Job portals
- Classified listings
It seems safe to use the convenience, but then one platform spills your information.
Why This Is a “Single Point of Failure”
In cybersecurity, a single point of failure means that a single weak connection can bring down the entire system. If you utilize the same number for all of your services, that number is the weakest link that everyone shares.
If it fails because of fraud, a telecom malfunction, or a data breach, everything that depends on it becomes unstable. OTP-based security makes this risk even more serious because so many systems rely on SMS verification.
Here’s how one failure spreads:
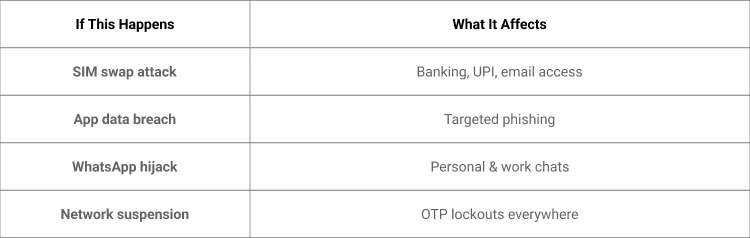
The risk isn’t theoretical. It’s structural.
Scenario: What Happens When That Number Gets Compromised?
Most people don’t think about the consequences until something goes wrong. But once your number is compromised, recovery becomes stressful and time-consuming.
Because your number links multiple accounts, attackers don’t need full access to everything they only need one vulnerability to begin exploiting connected systems.
Let’s look at how this works in real life.
Scenario 1: Attack on SIM Swap
A scammer calls your phone company and gets them to send you a second SIM card.
Suddenly:
- You stop receiving OTPs
- Your banking app logs you out
- Password reset codes go elsewhere
- UPI transactions can be attempted
Meanwhile, the attacker begins receiving your OTPs. Password resets become possible. Banking apps may be re-verified. Your email recovery system can be targeted.
Within minutes, your financial ecosystem can be exposed to all because one number controls everything.
Scenario 2: You Posted Your Number on a Marketplace
You shared your number publicly to sell an item online. At first, nothing seemed unusual. Then the spam begins.
Bots scrape your number, added to marketing databases, and possibly sold to phishing groups.
Within weeks:
- Spam calls increase
- Fake “KYC update” messages arrive
- WhatsApp investment scams start
- Telemarketers never stop calling
Now imagine that the same number is tied to your bank, UPI, and primary email. A simple classified listing becomes an entry point for broader targeting.
For deeper insight into privacy protection, you can explore how to enhance privacy with a second phone number on Second Line Number’s blog.
Scenario 3: One Number for Social + Banking + Apps
You use the same number for:
- Dating apps
- Grocery deliveries
- Ridesharing
- Government registrations
- Financial services
That feels convenient until one platform suffers from a data leak.
Attackers now have your name, location, and number. With that information, they can craft convincing, personalized phishing attempts.
This is not a business risk. It’s an everyday personal life risk something most competitors overlook when discussing phone number management.
Competitors Focus on Business. Here’s What Actually Matters
Most discussions about second numbers revolve around sales teams, entrepreneurs, or call centers. The focus is branding and professional separation.
But everyday users face different risks of privacy leaks, harassment, spam escalation, and identity fraud. Students posting rental listings, parents sharing numbers on school forms, gig workers interacting with customers, these are high-frequency exposure points.
For example, gig drivers often deal with post-delivery contact issues, which is why safety-focused discussions like the guide on gig driver safety at Second Line Number matter beyond business use cases.
The Safer Model: Number Segmentation
Number segmentation is a simple strategy: divide usage based on sensitivity. Not all platforms deserve access to your core identity number.
By separating essential services from public or temporary interactions, you reduce the “blast radius” of any compromise. Recovery becomes easier, and exposure becomes contained.
Here’s a practical breakdown:
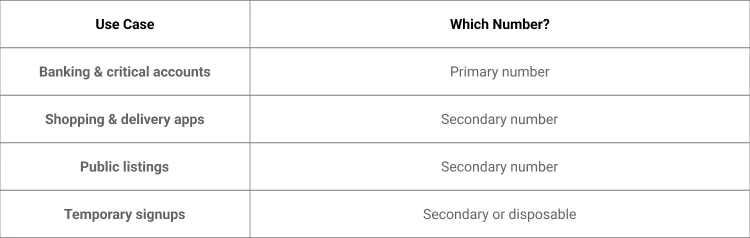
If you’re unsure how to set this up, guides on how to get a second line phone number walk you through the process step-by-step.
How a Second Line Protects Everyday Life
The second number isn’t about complexity. It’s about control. You can be flexible without changing your Primary SIM or telecom provider.
With a service like Second Line Number, you can set up a separate way to connect individuals for activities that are open to the public. If it gets too much spam, you can control or replace it without affecting your main accounts.
This is helpful for:
- Online marketplaces
- Delivery services
- Apartment hunting
- Dating apps
- Freelance gigs
If you’re trying to decide between different possibilities, knowing the virtual vs traditional phone numbers will help you see why app-based solutions are more flexible.
Comparison: One Number vs Two Numbers
The difference between one number and two numbers isn’t about convenience; it’s about containment. When risk is distributed, the impact is reduced.
Here’s how the models compare:
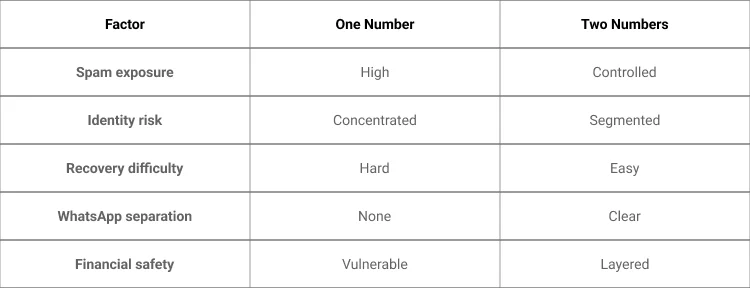
Clear Takeaways
Your phone number is no longer just a communication tool; it’s an authentication gateway. When you use one number for everything, you centralize risk.
A single compromise can affect banking, messaging, email recovery, and app access. Segmentation cuts down on exposure significantly.
The second number is not beyond the acceptable range. It’s structured protection for modern digital living.
Frequently Asked Questions
1. Is it safe to use one phone number everywhere?
No. If that number is hacked, it could damage all of your associated accounts, including your banking and recovery systems.
2. Should I have more than one phone number?
Yes. Putting important accounts out of public view reduces the risk of identity theft and fraud significantly.
3. Is it possible for someone to hack my bank with my phone number?
Not directly, although SIM swap attacks can get OTPs and let you reset your credentials.
4. What is a SIM swap attack?
It’s when a scammer swaps your number onto another SIM card so they can access your messages and codes to verify your identity.
5. Why do scammers want my phone number?
Your number allows them to send phishing messages, impersonate services, and attempt account verification fraud.
6. Is a second phone number legal?
Yes. Virtual second numbers are legal when used for communication and privacy protection.
7. Is it possible to use a second number with WhatsApp?
Yes. Many people have separate WhatsApp accounts for personal and public use.